
Only a few years ago, the inevitable shift to all things Cloud was met with guarded optimism. But today, the shift is really happening.
- By Christian Morin
- Dec 01, 2017
Because Involta houses an organization’s most critical equipment and disseminates highly sensitive data, their facilities required a layered approach to their security solution—including access control, video surveillance, wireless locks and more—to ensure access is granted only to the appropriate person.
- By Ellie Randall
- Dec 01, 2017
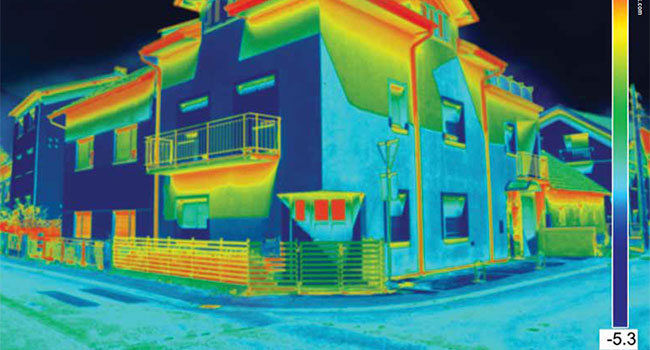
As video manufacturers have been driven to differentiate themselves in the marketplace, high-end surveillance technologies have become accessible to a much broader customer base. One technology of note is thermal imaging.
- By John Distelzweig
- Dec 01, 2017

The 300,000 person Fremont Festival of the Arts, one of the largest street festivals west of the Mississippi River and toted as California’s premiere art, wine and music festival, is no small undertaking. The threat of an attack is a real possibility.
Should more parishioners carry guns in church? Texas Attorney General Ken Paxton says yes, because as he sees it: “This is going to happen again.”
- By Ralph C. Jensen
- Dec 01, 2017
Some of the industry trends which have affected technology and deployment design include a dramatic cost reduction in entry level NVRs and cameras.
- By Brian Carle
- Dec 01, 2017

NYPD increased the security measures for this year’s Christmas tree lighting due to heightened vigilance in the wake of the truck attack in Tribeca in October.
- By Jessica Davis
- Nov 30, 2017

Police and a sheriff’s SWAT team raided the room and the suspect died shortly after being taken into custody.
- By Jessica Davis
- Nov 30, 2017
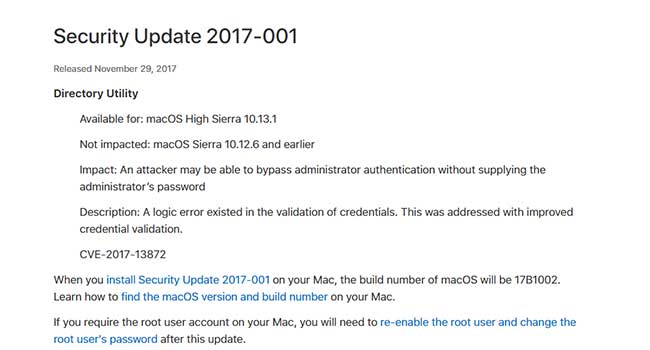
Apple has patched a macOS High Sierra flaw that would allow intruders to gain full administrator access on your system.
- By Jessica Davis
- Nov 30, 2017

A California man was arrested Sunday after he allegedly piloted a drone over two NFL stadiums in an attempt to distribute “anti-media” pamphlets to the crowds below.
- By Jessica Davis
- Nov 29, 2017

Being online puts you and your data at risk, but there are ways you can minimize your risk and make a hacker’s job harder.
- By Jessica Davis
- Nov 29, 2017
While temporary workers help serve the influx of holiday shoppers, they also represent higher security risks.

The center, which cost more than $5 million, is part of a citywide public safety plan.
- By Jessica Davis
- Nov 28, 2017

Christmas markets in cities across Germany are increasing their security this holiday season after the deadly truck attack at a market in Berlin last December.
- By Jessica Davis
- Nov 28, 2017

As you’re browsing for deals from your living room couch, keep security in mind.
- By Jessica Davis
- Nov 27, 2017

With hacks, attacks, ransoms and even extortion attempts, 2017 has been the year of data breaches, and it’s not even over yet.
- By Ankur Laroia
- Nov 24, 2017

No enterprise can eliminate 100% of its risk. Instead, the security objective must be to understand all risks and to effectively manage and mitigate them.
- By Simon Morgan
- Nov 22, 2017

The Transportation Security Administration expects more than 2.4 million passengers per day to pass through their checkpoints nationwide as people travel in the days leading up to Thanksgiving.
- By Jessica Davis
- Nov 21, 2017