
DP World Yarimca, one of the largest container terminals of the Gulf of İzmit and Turkey, is a strong proponent of using industry-leading technology to deliver unrivaled value to its customers and partners. As the port is growing, DP World Yarimca needs to continue to provide uninterrupted operations and a high level of security.To address these challenges, DP World Yarimca has embraced innovative technological products, including FLIR's comprehensive portfolio of security monitoring solutions.
From bustling urban centers to quieter suburban districts, businesses of all sizes and industries find themselves entangled in a complex web of criminal activities that threaten their stability, profitability, and sense of security.
- By Eric Lipson
- Dec 05, 2023
Transportation is an essential industry that enables goods and products to be transported efficiently and effectively across state and country lines. However, the transportation industry is not immune to security incidents.
- By Robert Wall
- Aug 01, 2023
Power is a lifeline, a critical component for connected products and devices in the physical security, access control and loT industries. We know how important it is to have in our everyday lives – and for the critical infrastructure, 24/7 power is a mandate for life safety.
- By Michael Bone
- Jul 07, 2023

Over three-quarters (77%) of organizations across US critical national infrastructure (CNI) have seen a rise in insider-driven cyber threats in the last three years, according to new research by leading cyber security services firm Bridewell.

Hazardous areas within industries like oil and gas, manufacturing, agriculture and the like, have long-sought reliable video surveillance cameras and equipment that can operate safely in these harsh and unpredictable environments.
- By Joe Morgan
- Mar 24, 2023
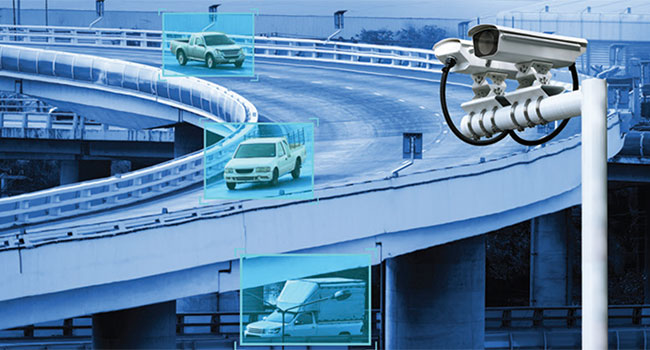
One of the biggest drawbacks to living and working in modern cities is traffic congestion. It frustrates motorists. It increases the probability of accidents. It can slow response time for emergency services. And, it lowers air quality.
- By Kevin Taylor
- Sep 19, 2022

Critical infrastructure facilities can be quite large, so protecting them is a complex challenge that demands multifaceted solutions. Robust, cybersecure technology solutions exist to protect facilities of all sizes and types but getting the most out of these solutions requires attention to the human element as well.
- By Greg Kemper
- Jul 29, 2022

In recent years, we’ve seen an influx of cybersecurity threats compromising energy players, from Saudi Aramco in 2012 to the Colonial Pipeline last year, both of which have had the power to halt the flow of fuel to entire states and nations. In fact, a 2019 survey of global utilities by Siemens and the Ponemon Institute showed 56% of respondents reported that, in the last 12 months, their organization experienced at least one attack that resulted in the loss of private data or an outage.

Outside of physical attacks, when natural gases are extracted, transported, and refined, invisible gas leaks pose a quieter and consistently costly threat. In fact, the United States oil and natural gas industry loses approximately 1.4 to 2.3 percent of its natural gas from operations due to leaks, each year, according to the EPA.
- By Kai Moncino
- Mar 01, 2022

In the new world of modern industrial networking solutions, the security measures to protect a network must match the pace of innovation across many industries, including mining, oil and gas, agriculture, transportation, heavy construction, military, municipalities, and government.
- By Chris Wall
- Aug 02, 2021

The last 12-18 months have shown us just how important our nation’s infrastructure is to our daily lives as well as our health and safety.
- By S. Guerry Bruner
- Aug 02, 2021

U.S. Customs and Border Protection agriculture specialists at the Pharr International Bridge discovered a rare pest, a first in nation discovery, in a shipment of coconuts.

When it comes to device and systems connectivity, surge protection solutions can mitigate risk
- By Chris Ralston
- May 20, 2021

Utility and industrial enterprises need secure operations around-the-clock, knowing that any threat to the public’s safety can negatively impact revenues and tarnish their reputations.
Federal, state and local agencies prioritize robust physical security plans for the nation’s electric power utilities. And they should. Any disruption in service from a primary provider could impact millions of people and businesses over a wide swath of the country.
- By John Nemerofsky
- Dec 03, 2020
Networked devices have made all the difference in giving security and communication systems far more ubiquity, capabilities, and performance than anyone could have dreamed of when the IP was invented in 1974.
- By Ronnie Pennington
- Oct 06, 2020
The Maryland Department of Transportation Maryland Port Administration (MDOT MPA) was awarded $1,158,589 in the most recent round of the Federal Emergency Management Agency’s (FEMA) Port Security Grant Program.

The Energy Department will form a task force focused on identifying and banning equipment that pose national security risks.
- By Haley Samsel
- May 06, 2020

How to improve client and employee trust, collaborate across departments and reduce costs through SOCs
- By Gilad David Maayan
- Apr 07, 2020